Most people don't realize that every command they type in a Linux terminal gets saved to a file. Passwords, API keys, SSH connection strings, config file edits — all of it sitting there, quietly logged, waiting to be read.
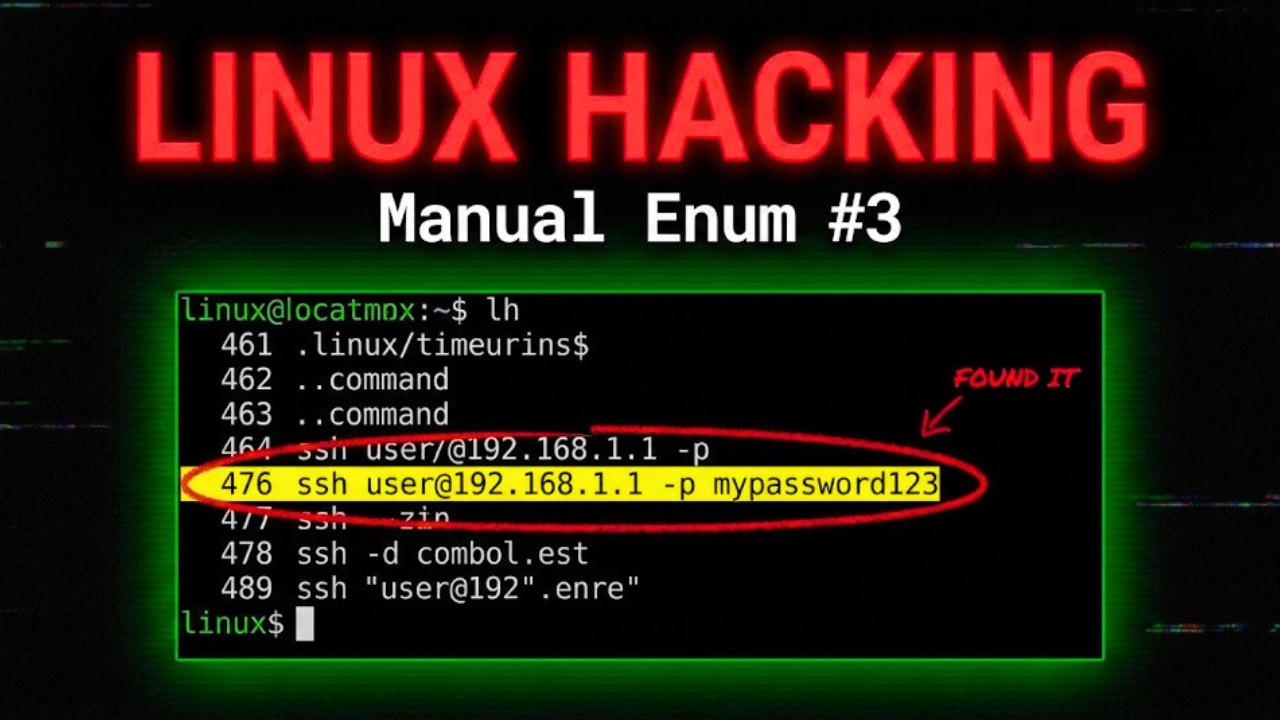
In this video we dig into bash history enumeration. As a hacker who just got initial access to a Linux machine, one of the first things you do is check what commands the previous user ran. Why? Because developers and admins are creatures of habit — and careless ones type credentials directly into the terminal all the time.
We cover the `history` command, where `.bash_history` and `.zsh_history` files actually live, how to read history for other users on the system, and how to use `grep` to quickly filter for passwords, SSH keys, and anything else valuable buried in hundreds of commands.
This is part 3 of the Linux Manual Enumeration series. Links to part 1 and 2 are in the description below.
TIMESTAMPS
0:00 – Intro: enumerating terminal history
0:56 – Why bash history is valuable for privesc
1:52 – Admins often type passwords directly in the terminal
2:14 – What else history can reveal: API keys, config paths, backups
2:37 – Live demo: running the history command
3:12 – Using grep to hunt for specific keywords
3:27 – Where history files are stored & using ls -a for dotfiles
4:16 – .zsh_history vs .bash_history — shell matters
4:52 – Reading history with cat & checking other users
5:37 – Trying to read root's history — permission denied
5:48 – Using sudo to access root's bash history
6:33 – What's next: system information enumeration
TOPICS COVERED
linux privilege escalation | bash history enumeration | linux hacking | manual enumeration linux | finding credentials in bash history | linux privesc | ethical hacking linux | kali linux tutorial | .bash_history linux | .zsh_history linux | linux post exploitation | grep for passwords linux | linux terminal history | linux initial access | CTF privilege escalation | red team linux | linux hidden files | linux dotfiles | linux credential hunting | cybersecurity tutorial
TAGS
linux hacking tutorial,penetration testing linux,cybersecurity tutorial,linux security,linux privesc tutorial,linux hacking 2025,history command linux,cat bash history,linux manual enumeration,linux user enumeration,linux api key hunting,linux password enumeration,linux privilege escalation for beginners,ethical hacking tutorial,linux command line hacking,post exploitation linux,linux root access,linux lateral movement

















Информация по комментариям в разработке