100% FUD Bypass: New Crypter Method for APK & Windows Executables – Threat Analysis & Security Research (2026)
Android-related telegram: t.me/Clicksssstam
PC-related telegram: t.me/Clicksssstam
Website : https://apkprotection.shop
Important Disclaimer & Legal Notice
This video is strictly for educational and security research purposes only. All demonstrations are conducted in a fully isolated, controlled lab environment (sandboxed VM with no real-world impact).
Misuse of these techniques for unauthorized access, malware distribution, or any illegal activity is strictly prohibited and punishable by law.
We do not provide downloads, tools, or encouragement for malicious use. This is cybersecurity awareness content to help defenders understand evolving threats.
In this deep-dive analysis, we examine an advanced FUD (Fully Undetectable) crypter method claimed to work on Android APKs (and reportedly Windows executables) in 2026. We break down its workflow, test real-world detection claims (e.g., 0/60 on VirusTotal), and — most critically — explain how to detect and defend against such stealthy evasion tactics.
What You’ll Learn in This Video:
🔍 Overview of the "secret" FUD crypting process for Android APKs
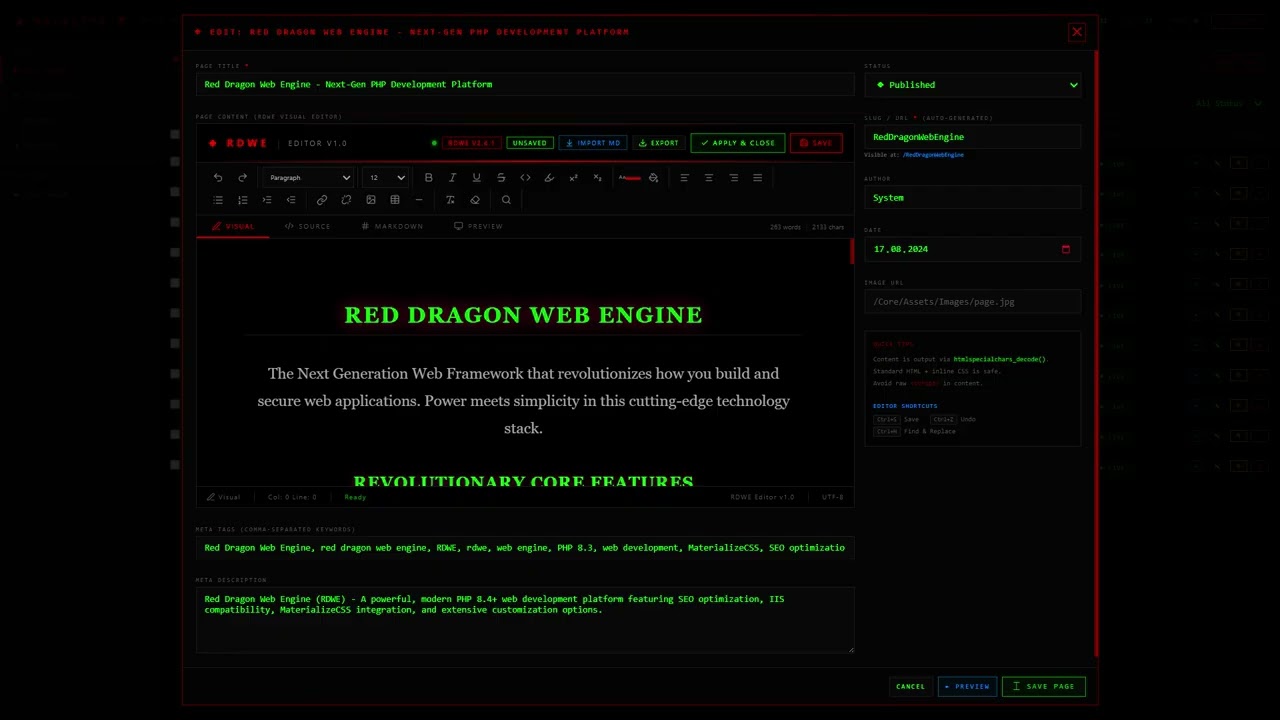
⚙️ Step-by-step walkthrough: setup and usage in a secure, sandboxed environment
🧪 LIVE TESTING: Uploading the crypted APK to VirusTotal, MetaDefender, and other major scanners
📊 Honest results breakdown: Does it truly achieve 0 detections in 2026?
🛡️ Security Focus: How modern Android malware evades detection — and proven defenses
📲 Best practices for mobile security: Strengthening Google Play Protect, safe habits, and user awareness
This is NOT a hacking tutorial.
It’s designed for:
Aspiring ethical hackers & penetration testers
Cybersecurity students & professionals
Android users wanting to understand current mobile threats
🚨 Claimed Features (As Presented by Providers – For Awareness Only)
100% FUD – 0 detections on VirusTotal & similar scanners
Scantime + Runtime bypass – evades static & dynamic checks
Lightning-fast, no lags or suspicious behavior
Anti-sandbox, anti-emulation, anti-debugging techniques
Simple: Encrypt → Launch → Works
⚠️ Important Reminder
Tools and methods like this are only for authorized red-team/pen-testing with explicit written permission. Unauthorized use is a serious crime.
We do not link to, endorse, or distribute any crypters, download links, or services.
Resources Mentioned (For Research/Reference Only – Verify Independently):
Android-related channels/groups: t.me/Clicksssstam
PC-related: t.me/Clicksssstam
Website example: https://apkprotection.shop
Keywords for Search Optimization:
Bypass PlayProtect, Play Protect bypass 2026, 3Click APK FUD, FUD Crypt tutorial, APK FUD crypt, Undetectable APK, Bypass Google Play Protect, APK modding guide, Android bypass PlayProtect, FUD APK crypt, PlayProtect evasion, APK injection bypass, Android hacking tutorial, Modded APK install, Google Play Protect disabled, APK obfuscation, Ethical hacking APK
Hashtags:
#AndroidHacking #UndetectedMalware #Crypter2026 #FUD #CyberSecurity #HackingTools #BypassAV #EthicalHacking #PlayProtectBypass #APKBypass #FUDCrypt #APKMod #AndroidHack #ModAPK #BypassPlayProtect #APKTutorial #FUD #AndroidModding #HackingTutorial #TechHacks #CyberSecurity #APK2026 #UndetectableAPK #PlayProtect #AndroidTips #EthicalHacking #Viral #Trending #ReverseEngineering
Ask in comments: #ApkFudCrypter or share your thoughts on modern evasion techniques (keep it educational/legal)!




















Информация по комментариям в разработке