Attackers aren’t breaking in—they’re blending in. In under a minute, this video shows how native phishing abuses trusted Microsoft 365 tools (OneNote, OneDrive, real sharing emails) to steal credentials—and how to stop it.
What you’ll learn
Why native phishing looks normal but acts malicious
How OneNote links/embeds + real Microsoft notifications enable deception
The attack chain: Compromise → OneDrive share → OneNote → fake login
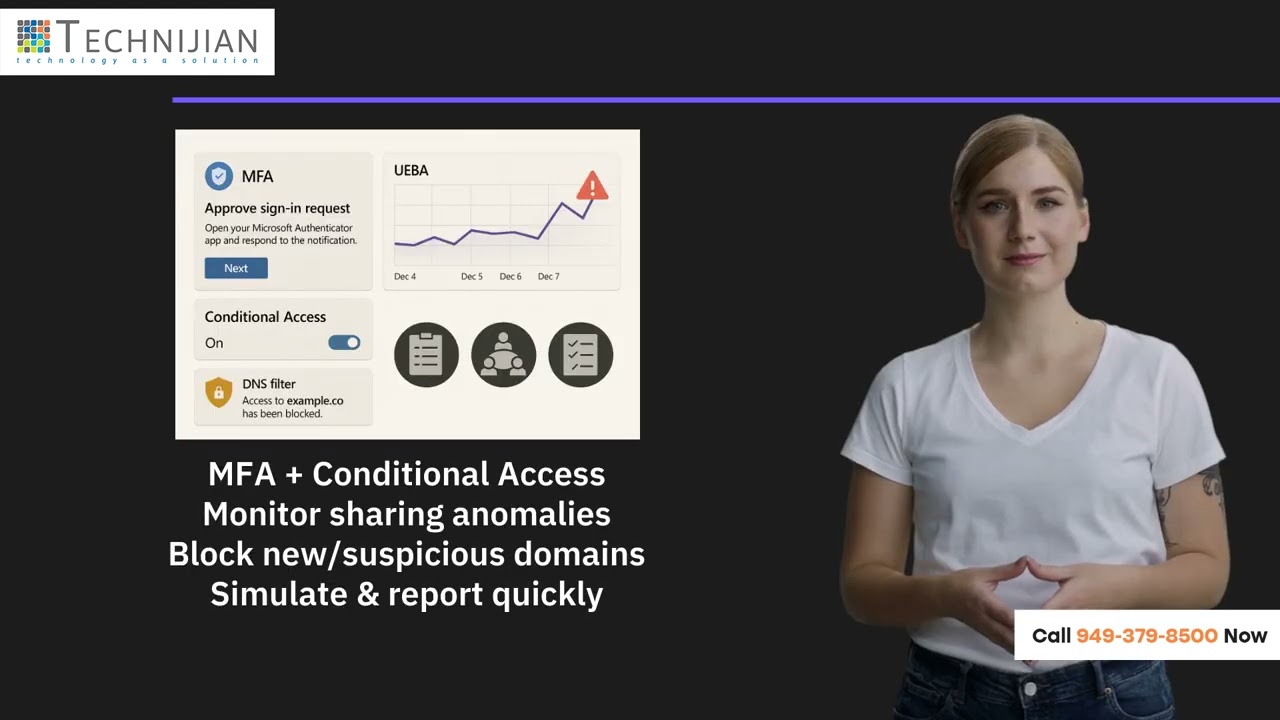
A layered defense: MFA, Conditional Access, UEBA, DNS filtering, realistic training.
📖 Read the full blog:
https://technijian.com/cyber-security...
🎙 Listen to the podcast:
https://technijian.com/podcast/native...
Timestamps
00:00 Awareness — Phishing inside trusted apps
00:10 Escalation — OneNote links, fewer prompts, real Microsoft emails
00:20 Tactics — Compromise → Share → Harvest (AI-built look-alikes)
00:33 Protection — MFA, Conditional Access, UEBA, DNS filtering, simulations
00:48 CTA — Technijian: monitoring, analytics, simulations, incident response
Defender’s checklist
Enforce MFA everywhere + Conditional Access (device posture, impossible travel)
Monitor for unusual sharing spikes and anomalous sign-ins (UEBA)
Block newly registered/suspicious domains at DNS
Simulate native phishing and tighten incident reporting SLAs
Work with Technijian
We harden Microsoft 365 with 24/7 monitoring, behavioral analytics, native-phish simulations, and rapid incident response.
Disclaimer: Educational content only. Do not attempt unauthorized access.
✨ Like, Share, Comment, & Subscribe! ✨
Stay updated with our latest videos, tips, and insights by subscribing to our YouTube channel!
🔔 Don't forget to hit the notification bell to never miss an update!
#Cybersecurity #Phishing #Microsoft365 #OneNote #OneDrive #UEBA #MFA #ConditionalAccess #DNSFiltering #ZeroTrust #IncidentResponse #SOC #technijian
native phishing, microsoft 365 security, onenote phishing, onedrive phishing, microsoft sharing email scam, credential theft, business email compromise, account takeover, ai phishing, no-code phishing, phishing simulation, conditional access, mfa, ueba, dns filtering, zero trust, identity protection, microsoft entra id, azure ad, cloud security, security awareness training, incident response, soc monitoring, technijian, url verification, fake login page
🌐 Visit Us: https://technijian.com/
💻 Follow Us on Social Media:
➡️ Facebook: / technijian01
➡️ Instagram: / technijianinc
➡️ LinkedIn: / technijian
➡️ TikTok: / technijian
➡️ Pinterest: / technijian01
➡️ X (Twitter): / technijian_
🎙️ Subscribe to Our Podcast Channel:
🎧 Spotify: https://open.spotify.com/show/6dUhKMR...
📺 YouTube Playlist: • Technijian
🎶 Amazon Music: https://music.amazon.com/podcasts/623...

![[4K FULL HD] Relaxing Water Background | 1 HOUR | Calm Water Wallpaper (No Sound)](https://i.ytimg.com/vi/y9PTNTSpGJs/maxresdefault.jpg)
















Информация по комментариям в разработке