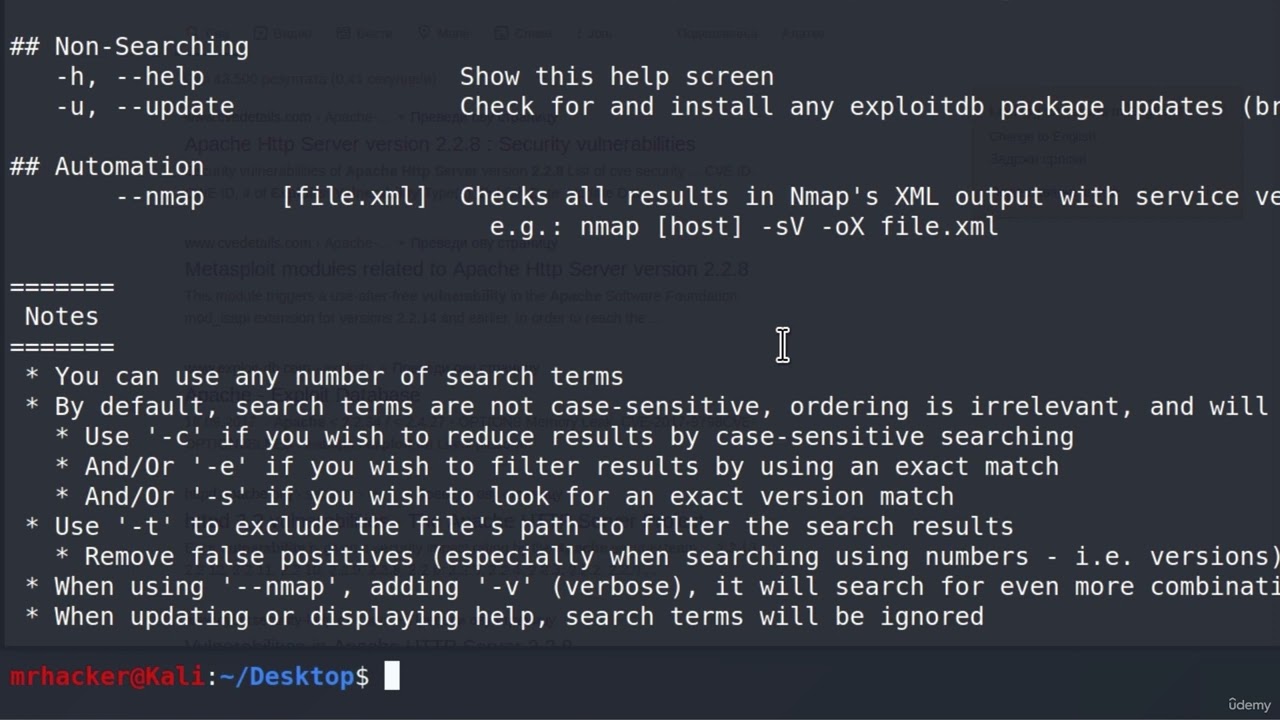
Скачать или смотреть 36 Manual Vulnerability Analysis & Searchsploit - Expanding Your Security Assessment Toolkit
-
2023-06-16
-
2562
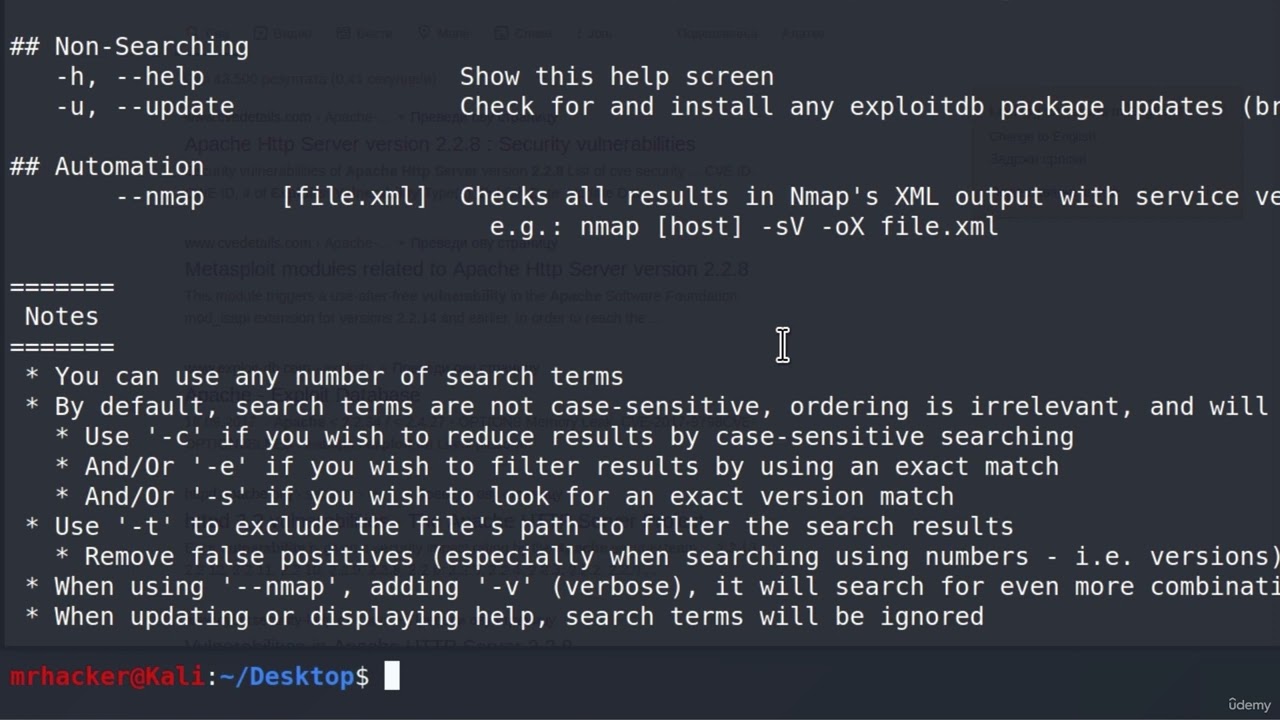
Скачать 36 Manual Vulnerability Analysis & Searchsploit - Expanding Your Security Assessment Toolkit бесплатно в качестве 4к (2к / 1080p)
У нас вы можете скачать бесплатно 36 Manual Vulnerability Analysis & Searchsploit - Expanding Your Security Assessment Toolkit или посмотреть видео с ютуба в максимальном доступном качестве.
Для скачивания выберите вариант из формы ниже:
-
Информация по загрузке:
Cкачать музыку 36 Manual Vulnerability Analysis & Searchsploit - Expanding Your Security Assessment Toolkit бесплатно в формате MP3:
Если иконки загрузки не отобразились, ПОЖАЛУЙСТА,
НАЖМИТЕ ЗДЕСЬ или обновите страницу
Если у вас возникли трудности с загрузкой, пожалуйста, свяжитесь с нами по контактам, указанным
в нижней части страницы.
Спасибо за использование сервиса video2dn.com
Информация по комментариям в разработке